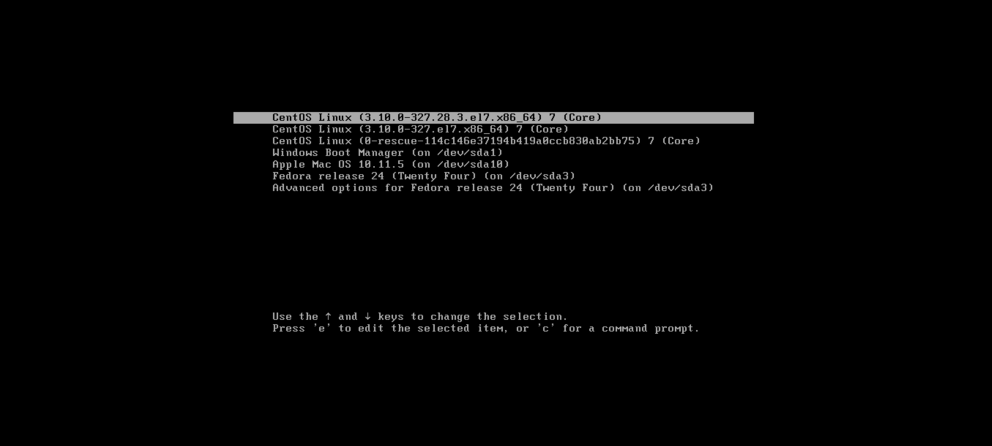
A flaw in the GRUB2 bootloader affects most Linux devices and some Windows computers using UEFI Secure Boot.
First of all, What is a UEFI secure boot?
UEFI Secure Boot (SB) is a verification mechanism for ensuring that code launched by a computer’s UEFI firmware is trusted. It is designed to protect a system against malicious code being loaded and executed early in the boot process before the operating system has been loaded.
The boot process is critical to securing any device. It relies on a variety of firmware to initialize and control different components of a machine, and it coordinates how the OS is loaded.
What is the issue?
Unfortunately, a serious bug has been found in the GRUB2 bootloader code. It reads and parses its configuration (grub.cfg). This bug breaks the chain of trust. By exploiting this bug, it is possible to break out of the secured environment and load non-signed programs during early boot. This vulnerability was discovered by researchers at Eclypsium who named it Boothole.
A hacker may install unwanted firmware and software and gain access over your computer. You may not know it at the start but once you start noticing something fishy, it will be too late to act. The attacker will have complete control over your machine.
While GRUB2 is the primary bootloader for modern Linux distros, this bug affects systems using Secure Boot even if they’re not using GRUB2.
The fix to the problem?
The fix is simple, update the GRUB2 bootloader, update the firmware, shims, but the scale of this issue is huge. Fixing this problem may take a lot of time. This is a worldwide issue now. It may take years to completely get rid of this issue. It will require co-ordinate efforts from the users who are affected by this, open-source projects, etc.
“It’s sort of bad when fixing the problem is a problem, and this is one of those instances,” says Loucaides of the complexity of patching BootHole.
In response to Eclypsium’s initial report, Canonical researchers looked at GRUB2 with greater scrutiny and found additional vulnerabilities. An industrywide effort is underway to identify and fix more vulnerabilities that don’t yet have individual CVEs assigned.